Memory Corruption is a very common word related to computer errors, Most of the low-level errors happen due to memory corruption. In the Computing sense, the word corruption means errors in the data during reading, writing, processing, transmission, or storage of the data. Unexpected behavior of programs, crashing of the operating system, loss of valuable data can take place as a result of memory corruption. if happened at the wrong state of a computing operation, memory corruption can cause a lot of severe damage to the user data and may also lead to system failure.
Contents
Reasons of Memory Corruption
There could be many potential reasons for such corruption errors. Most of the time, memory corruption errors are resolved at the developer end, most of the bugs are determined at the testing phase. But not all corruptions are caused by bugs. There could also be physical reasons, intentional reasons such as malware or viruses, etc.
Due to bugs

The most common reasons for corrupt memory are bugs in the programming. Most kernel-level programming of an operating system is done in the C/C++ language. Both of these programming languages have explicit memory management using pointer arithmetic. A pointer is a particular type of variable that stores the memory address of another variable. If the memory management is done inefficiently using the pointers inappropriately, then the program may lead itself to memory corruption.
Bugs caused by improper pointer arithmetic could be highly complex because the fault that occurred due to the buggy code may be far away from where it was source code, making it hard to relate and find the source of the problem. It could be a real hassle for the developers to work around a complex program code with memory management-related issues. It is advised for users to use well-documented and developed applications.
Due to malware
Some programs are explicitly made by attackers or hackers that may corrupt your memory. It is essential to save your system from such malware as the consequences could be catastrophic. The most common type of attack is the BOA(Buffer Overflow Attack).
In buffer overflow attacks, malware is specifically programmed to outgrow the memory space that it has been allotted by the Operating System. The malware intentionally tries to enter the adjacent memory that might have been assigned to another program. This results in the corruption of data in the overlapping memory space.
Other reasons
Apart from bugs or malware, other potential reasons could corrupt the system memory. These reasons can be utterly random on which neither the developer nor the user can have any control. The followings are some potential causes of memory corruption.
- Any sort of physical damage to the memory device can cause corruption.
- Insufficient power supply to the memory device could result in data loss. especially in the case of DRAM.
- Dynamic Random Access Memory (DRAM) is built using capacitors that needs to be recharged constantly, hence fluctuations in the oprerating voltage could sometimes lead to curroption of memory.
- A malfunctioning I/O device or peripheral can be responsible for corrupt data in the working memory.
File or storage corruption
People seem to use the terms memory corruption and data corruption interchangeably. While both are almost similar topics, there are still some differences. Disk data corruption is Storage corruption. It is the corruption of the data that is permanently stored in the system’s hard drive. The most common reasons for this corruption are physical damage, hardware failure, improper startup or shutdown, sudden power outage, or malware. The data in the disk, such as files, images, music, documents, etc., and the whole file system of the disk, can be severely damaged in this kind of corruption.
Difference between file and memory corruption
Although data corruption is the word that can be used universally for any kind of corruption in the computing jargon, the following terms can still be classified for the sake of terminology.
| Memory corruption | File corruption |
|---|---|
| This term is used regarding the corruption of data currently loaded in the working system memory. (RAM) | This term is used for the corruption of data that is permanently stored in the storage device’s file system (hard disk). |
| Consecuences are immediate. | It might take some time to observe i.e. until the corrupted file is accessed. |
| This term should be used in the case of volatile memory. | This term should be used for non-volatile memory. |
| The comparatively small size of data is corrupted, i.e., data required by CPU for its computations such as OP codes or memory addresses. | Big files can be corrupted, such as documents, videos, images, etc. |
Memory Corruption in Linux
Linux is an open-source operating system kernel. There are many flavors of Linux. However, bugs are inevitable in computer programs, and users can also encounter a corruption of memory in Linux.
Debugging corrupt memory in linux
The first thing to do when debugging in Linux is to check the system log files. Log files contain helpful information about all the processes running on the system from startup. In Linux, log files are stored in the “var/log” directory. Reading the log files can reveal crucial information about memory leaks in the system, which can be used later for debugging purposes.
Using valgrind
Valgrind is a free and open-source instrumentation framework that can automatically detect bugs related to memory management. Valgrind was supposed to be a free memory debugging tool for developers, but now it has evolved as a mature framework for memory profiling. You can download the latest release of Valgrind from here.
After downloading and installing Valgrind, you can test the program for memory leaks and then read the output of the test for further debugging the program’s source code.
valgrind --leak-check=yes program_name program_arguementsWhere program_name is the program’s name you want to test for memory corruption, and program_arguements can be an arbitrary number of inputs that the program takes in.
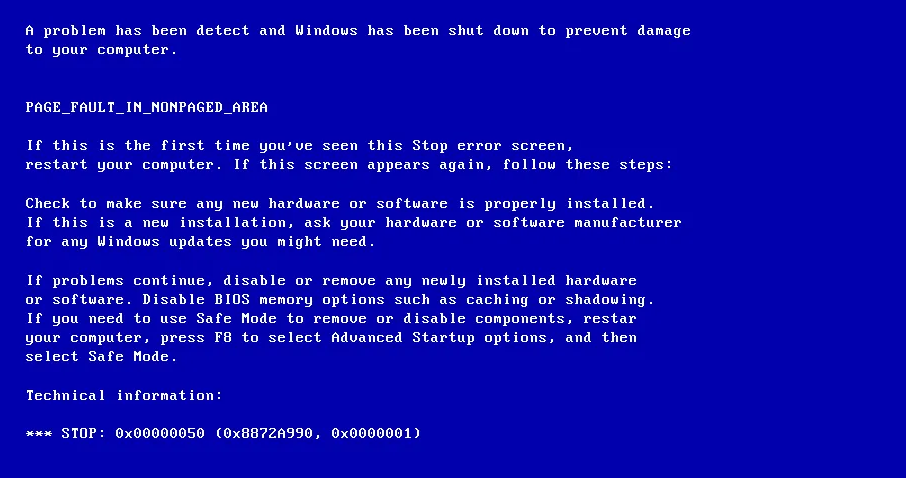
Memory corruption in low memory
“memory corruption detected in low memory” this message is logged in the kernel logs whenever there is a corruption of memory at the low level. The Linux kernel saves 64K of system memory for the Basic Input Output System (BIOS). If there is any unexpected change in that reserved part of the memory, then an error message is logged in the system log.
If you are facing this issue on your machine, a BIOS update is the best way to get through this. Check your motherboard and download the latest compatible BIOS from the manufacturer’s website and update it.
malloc() memory corruption
The malloc() is a function in the C/C++ language used for dynamic memory allocation. It takes several bytes as an input argument and returns a pointer to the beginning of the allocated memory space of the given size. If not used properly, this function can result in the corruption of memory in the program.
If the amount of data is more significant than the allocated memory space, the data is overwritten to the corresponding adjacent space (memory that another program might use), causing memory corruption.
Prevention for Memory Error

The consequences of any data corruption could be disastrous for both the user and the system. Therefore it is recommended to take some measures to reduce the chances of data corruption on your computer. The following measures should be considered.
- Always use the latest official release of the daily-use application software.
- Keep you Operating System up to date.
- Keep you BIOS and firmware up to date.
- Prevent your memory device such as RAM from any kind of physical damage.
- Prevent your storage devices such as Hard Drives, Flash storage, USB stick from physical damage.
- Do not connect any broken or malfuntioning device to your computer, that might lead to unusual behaviour.
- Prevent your system from improper shutdown or startup.
- Make sure that your PSU(Power Supply Unit) is in good health.
- Avoid sudden power outage(ex. use UPS).
- Use Antivirus software to scan for malware that causes curroption related issues.
- Backup your important data.
FAQs on Memory Corruption
What are two kinds of RAM?
Two kinds of RAM are Static RAM and Dynamic RAM, SRAM is fully transistor-based while DRAM is capacitor-based.
What is a memory space?
It is the range of the memory addresses that a particular process is allowed to use.
What is paging?
It is a memory management scheme, in which data is retrieved from the secondary storage in form of blocks called pages.
What is memory corruption vulnerability?
It refers to the threat that might be caused by memory leaks, a malicious program could take advantage of this and could steal valuable data or execute binary code.